DApp-Architecture Primer
- all
DApp Architecture Primer
Introduction
Decentralized applications, or DApps, promise new models of trust, transparency, and resilience. But building a DApp is not just about writing smart contracts; it requires thoughtful architecture that balances on-chain guarantees with off-chain practicality. This primer walks engineers and technical founders through the core concepts, the common patterns, and the key trade-offs that shape scalable, secure DApps.
Whether you are pursuing a tokenized finance platform, a DAO-enabled governance tool, or a data marketplace, the architecture decisions you make in the early stages have a material impact on security, cost, and user experience. By the end of this guide you should be able to articulate a concrete architecture direction, justify it to stakeholders, and begin drafting an implementation plan.
What is a DApp?
A DApp, or decentralized application, is software that uses a blockchain as its backbone for trust and execution. Typically, the smart contracts run on a tamper-evident ledger, while the user interface (the client) interacts with those contracts via a web3 provider such as a wallet. Unlike traditional apps, the logic and data of a DApp are distributed, verifiable, and often open to public inspection.
There are multiple architectural flavors. Some DApps keep business logic on-chain for immutability and verifiability, others move compute off-chain to scale and reduce costs. The best pattern often combines on-chain guarantees with off-chain offloading for performance. The art lies in choosing where to put data, how to prove state, and how to secure the boundaries between components.
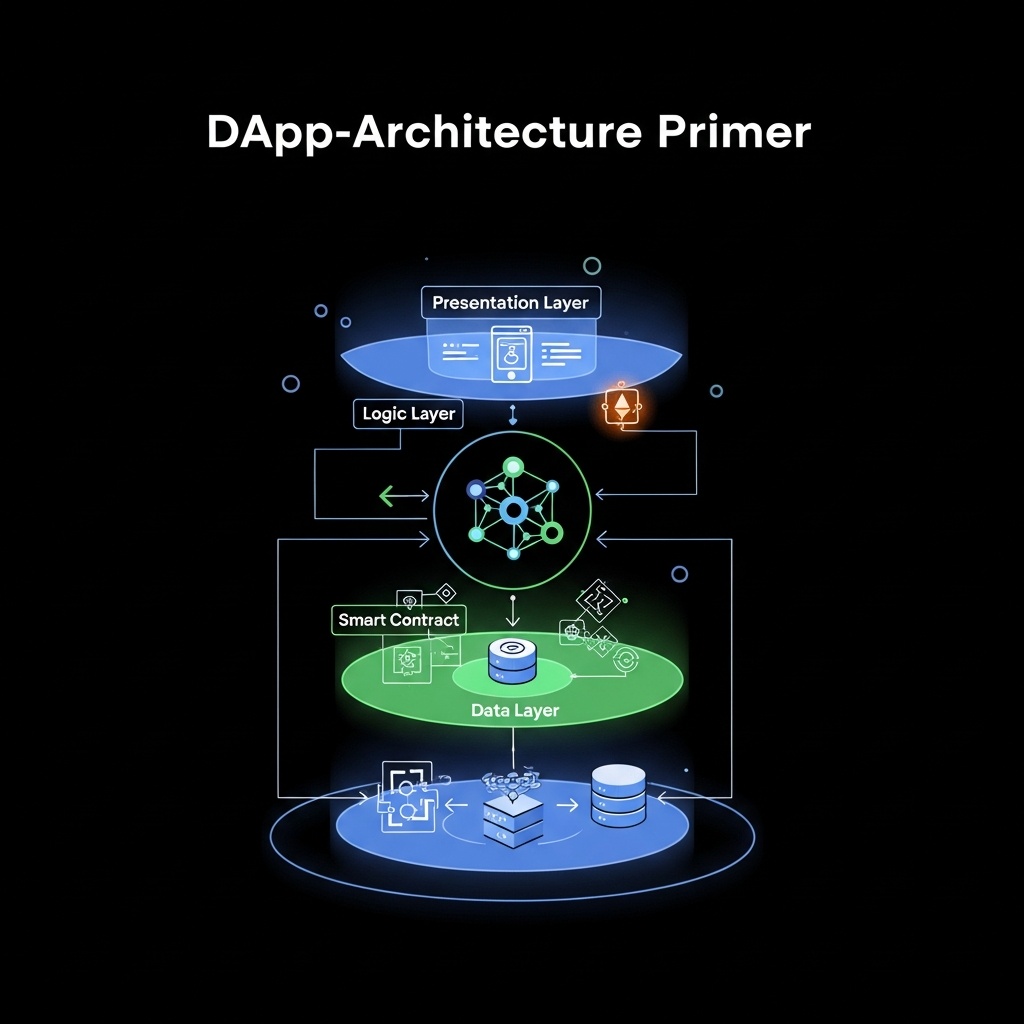
Architecture Layers
Think of a DApp as a stack with distinct layers: a client layer (the front-end), an on-chain layer (the smart contracts), and an off-chain layer (servers, indexing, and tooling). Each layer has specific responsibilities and failure modes. When designed well, they complement each other to deliver a secure, usable, and scalable product.
On-chain layer: smart contracts
Smart contracts encode business rules in a trust-minimized way. They are immutable (once deployed) and fee-bearing (gas costs). The on-chain layer should be compact, secure, and formally verifiable where possible. Developers should consider upgradeability, access control, and the potential for bugs that could be expensive or irreversible.
Off-chain layer: back-end and indexing
The off-chain components include centralized or decentralized back-ends, event indexing services, off-chain computation, and orchestration logic. Off-chain components can dramatically improve user experience and scalability by caching data, performing heavy computations, and handling integrations with external systems.
Client layer: web and mobile
The client layer provides a friendly user interface and connects to the blockchain through a wallet and a node provider or a service that offers a JSON-RPC API. The client also handles UX flows, onboarding, and error handling in collaboration with the back-end and the contracts.
Smart Contracts & Security
Smart contracts are the core of DApps, but they are only as secure as their design and testing. Practices such as formal modeling, defensive programming, and robust testing reduce risk. Design patterns such as proxies for upgradeability, library usage to minimize code, and clear access controls are essential.
Upgradeability and governance
Organizations frequently require upgrades. Upgradeable contracts use proxy patterns to separate logic from data. Be mindful of governance models, admin control, and potential single points of failure. Consider multi-signature governance and well-defined upgrade ceremonies that involve risk assessments and rollbacks.
Access control and permissioning
Role-based access control, time-locked functions, and pausable contracts are common safeguards. However, avoid over-complex permission trees that increase audit risk. Simpler, explicit authorization often wins in practice.
Data Storage & Privacy
Blockchains excel at immutable state, but not at storing large amounts of data. DApps typically store critical state on-chain and keep large payloads off-chain in databases or decentralized storage networks. IPFS, Filecoin, or ARweave offer content-addressable storage with verifiable integrity. For sensitive data, ensure encryption and access controls, possibly keeping PII off-chain and hashed on-chain where feasible.
Indexing and retrieval patterns matter for performance. Off-chain indexes can speed queries, but require syncing and robust data retention policies. Off-chain storage with cryptographic proofs ensures integrity while maintaining privacy and compliance requirements.
On-chain vs Off-chain Compute: Trade-offs
The central architectural decision for many DApps is what to run on-chain versus off-chain. On-chain execution offers trustless correctness and public auditability but incurs gas costs and lower throughput. Off-chain compute offers speed and cost efficiency but adds trust considerations and potential single points of failure. The best designs blend both worlds, keeping critical validations on-chain while outsourcing heavy processing and data storage to off-chain layers.
Practical guidance:
- Put business-critical, immutable rules on-chain.
- Move expensive computations off-chain and prove results on-chain when needed (zero-knowledge proofs, verifiable computation).
- Store large assets off-chain, with on-chain references (content-addressable hashes).
Security Best Practices for DApps
Security must be baked into the design from day one. Begin with threat modeling, then apply a defense-in-depth strategy across all layers. Some foundational practices include secure authentication, robust input validation, and careful error handling to avoid leaking sensitive state.
Threat modeling and risk assessment
Identify attackers, entry points, and potential economic incentives for exploit. Map out the value flow and enumerate possible attack surfaces at every layer—client, network, contract, and off-chain components.
Secure coding and reviews
Adopt best practices for smart contracts: use tested libraries, minimize contract size, and avoid known vulnerability patterns. Implement strict access controls and test failure modes. Pair programming and formal reviews reduce the chance of critical bugs slipping through.
Testing & Audits
Testing a DApp is a multi-faceted activity: unit tests for contracts, integration tests across layers, fuzzing for unexpected inputs, and formal verification where feasible. Audits by independent security firms are indispensable for public facing systems. Continuous monitoring and post-deployment audits further strengthen resilience.
Tooling and workflows
Common tools include static analysis suites, linters, fuzzers, and test networks. A well-configured CI/CD pipeline should run tests automatically on every change, with automated security checks gating deployments.
Post-deployment security
After deployment, monitor for anomalies, implement upgrade processes, and prepare incident response playbooks. Transparent disclosure and responsible remediation are critical to sustaining trust in a decentralized ecosystem.
Architecture Trade-offs: A Practical Framework
Every DApp architecture decision comes with trade-offs. The framework below helps teams articulate and compare options on a shared basis.
Decision criteria
- Security vs. usability: more on-chain logic can strengthen trust but may complicate UX.
- Cost vs. performance: on-chain operations incur gas; off-chain solutions reduce cost but require trust in services.
- Upgradeability vs. immutability: proxies enable evolution but add new risk vectors; immutability reduces risk of code changes but makes updates harder.
Decision matrix: example scenarios
Scenario A: A governance token with on-chain voting and off-chain indexing. Pros: strong verifiability, transparent tokenomics. Cons: higher complexity and gas costs. Scenario B: A data marketplace with on-chain access control but off-chain data storage. Pros: lower on-chain data footprint; cons: requires secure off-chain storage and robust integrity checks.
From Concept to MVP: A 6-Step Roadmap
- Define the use case and governance: clarify who can participate and how decisions are made.
- Pick the right blockchain and tooling: select the platform that offers the right consensus model, security guarantees, and ecosystem.
- Draft the smart contract architecture: decide on data models, access control, and upgrade strategy.
- Design the off-chain components: APIs, indexing, and front-end integration strategies.
- Prototype the UX: design a clear onboarding flow and fail-safe error handling.
- Implement MVP with tests and security reviews: ensure automated testing and an independent security audit.
Upon completion, you will have a working MVP that demonstrates the core on-chain behaviors and the key off-chain capabilities. The MVP serves as a platform for user feedback, investor validation, and architectural refinements.
Conclusion
Crafting a robust DApp architecture requires balancing on-chain guarantees with off-chain practicality, aligning with a sound security posture, and designing for scalability from the start. By thinking in layers, adopting proven patterns, and embracing rigorous testing and governance, teams can move from concept to reliable, scalable decentralized applications.